Focus & Scope Author Guidelines Review Process Manuscript Template Publication Ethics Publication Frequency Open Access Policy Plagiarism Policy Editorial Board Processing Charge
Search
1 - 21 of 21 items
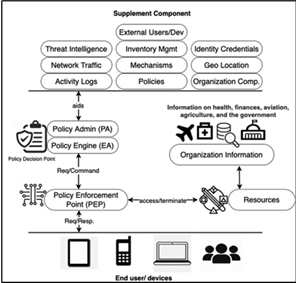
Zero Trust Architecture in Cloud Security: Enhancing Security Posture in the Cloud Era
Abstract : 224
PDF : 74
Assessment of RFID Implementation for Security in Electric Vehicle Charging Stations
Abstract : 79
PDF : 50
PiFortify: A Raspberry Pi-based Encryption Tool with Biometric Authentication
Abstract : 61
PDF : 63
Stegcryption: Graphical User Interface (GUI) Based File Protection System Utilizing Cryptography and Steganography
Abstract : 53
PDF : 64
Analyzing the Security Implications of Popular Video Conferencing Applications in Classified Environments: A Comprehensive Network Traffic Review
Abstract : 80
PDF : 44
Review of Network Intrusion Systems Evaluated on NSL-KDD and CIC-IDS2017 Datasets
Abstract : 89
PDF : 63
Securing e-commerce against SQL injection, cross site scripting and broken authentication
Abstract : 87
PDF : 60
Acrypt: Minimizing Data Leakage in Cloud Storage with Cryptography Encryption
Abstract : 60
PDF : 63
Simulation, Investigation and Response Towards Log4J Vulnerability (Log4Shell)
Abstract : 68
PDF : 86
Towards Inclusive Cybersecurity Learning: A Novice-Friendly Capture-the-Flag Onboarding Platform
Abstract : 87
PDF : 141
1 - 21 of 21 items